Imagine losing $50,000 overnight. It's not due to a bad investment, but because a cybercriminal infiltrated your systems.
While we'd love to keep it as a distant possibility, it is now a growing reality for many small businesses. With cyber security threats increasing daily, businesses must take proactive steps to defend themselves. Fortunately, you don’t need a massive IT budget to protect your company.
While we'd love to keep it as a distant possibility, it is now a growing reality for many small businesses. With cyber security threats increasing daily, businesses must take proactive steps to defend themselves. Fortunately, you don’t need a massive IT budget to protect your company.
By improving what the Australian Cyber Security Centre (ACSC) calls ‘cyber resilience,’ you can minimise risks, prevent costly breaches, and keep your business secure. In this article, join 1300 INTECH as we explore the following strategies in detail and offer actionable tips you can implement as a small to medium business (SMB) owner.
Common Data Breach Sources
Before we address the solution, it’s important to identify the root causes of these attacks. Doing so allows us to pinpoint what businesses like yours are lacking in most areas that we can potentially improve upon.
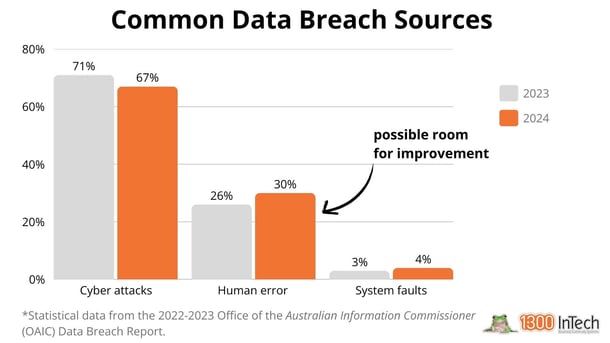
According to the 2023 Data Breach Report by the Office of the Australian Information Commissioner (OAIC), two-thirds of reported breaches were cyber attacks conducted by criminals. Human error accounted for one-third of breaches, with system faults ranking last.
While the high percentage of cyber attacks is to be expected, what’s most alarming here is the significant proportion attributed to human error. This only highlights the need for proactive measures SMB owners should take to strengthen their defences.
What does this mean? Many security incidents are preventable, but only if businesses take the right precautions.
What does this mean? Many security incidents are preventable, but only if businesses take the right precautions.
Essential cybersecurity measures to implement
With that said, the Australian Signals Directorate (ASD) recommends these essential steps to boost ‘cyber resilience’:
- Turn on multi-factor authentication
- Secure mobile devices
- Back up your information securely
- Update your software regularly
- Train your employees on cyber security best practices
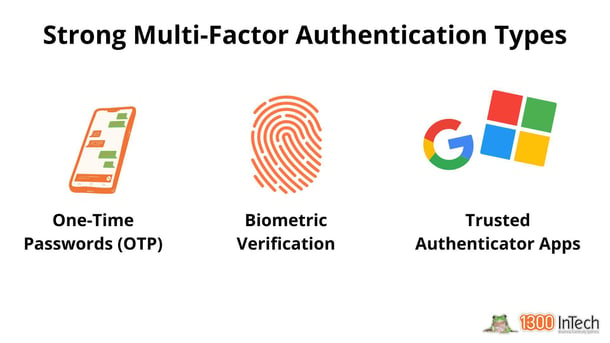
1. Implementing multi-factor authentication (MFA)
One of the most effective solutions is implementing multi-factor authentication (MFA). Implementing MFAs significantly reduces the risk of cyber criminals compromising your account.
You might be one of the many users who choose the ‘remember me’ option for convenience. However, this can pose a security risk, as hackers may exploit cookies to steal your login credentials and therefore breach your account.
While this feature is undeniably useful, there are steps you can take to reduce the risk of it becoming one of many cybersecurity threats criminal organisations could use against you.
2. Implementing mobile phone security
In the digital age, Australians are spending an average of 4.5 hours per day on their phones. As a business, it’s essential to meet your customers where they are most active — online.Equipping employees with these skills ensures they remain vigilant and prepared, strengthening your business's defence about the latest cyber security threats.
According to Verizon's 2024 Mobile Security Index (MSI) Report, mobile devices are vital for 80% of businesses surveyed, with 95% also integrating Internet of Things (IoT) devices into their operations. Note: Respondents comprise of people responsible for security strategy, policy, and management.
However, this heavy reliance on mobile technology makes small businesses like yours an ever-more appealing target for cybercriminals. Experts think so, too.
Alarmingly, 85% of respondents reported that mobile security risks have increased. Successful phishing attacks have affected 33% of technology firms, with over half experiencing system downtime as a result—leading to significant revenue loss.
Integrating your phone with MFA adds an extra layer of security, making it much harder for cybercriminals to gain unauthorised access. However, it's essential to remain cautious when downloading apps. Always verify that the app comes from a reputable source and download it only from trusted platforms to avoid potential cybersecurity threats from accessing them.
3. Implementing data backup protocols
Cybersecurity threats, particularly ransomware, continue to evolve at an alarming rate. Ransomware works by encrypting your data and demanding a ransom to unlock it, often threatening to leak business-sensitive information online if the demand isn’t met. Unprepared businesses often feel forced to pay, but this is where Magic Backups® comes in.
Backing up critical information should be a regular or automated practice in every business. Without consistent backups, your business is at risk of downtimes as you recover lost data.
With automated data backup and recovery systems, the beauty of Magic Backups® is that in the event of a cyber attack or data loss, you can restore your data without paying a ransom, even if the ransomware encrypts it. You can seamlessly restore your information pre-attack and continue operating your business as if nothing happened.
4. Updating outdated systems
Using outdated software and systems exposes your business to increased risks of cyberattacks. New software versions often fix bugs and security vulnerabilities that older versions still have. Many vendors eventually stop supporting legacy systems because maintaining them is resource-intensive.
Cybercriminals actively exploit these outdated systems, which is why updating your device is essential. A 20-minute downtime for an update is far preferable to losing thousands of dollars, hundreds of gigabytes of data, and countless hours due to an otherwise preventable breach.
If your device or software is no longer eligible for updates (referred to as legacy systems), we strongly recommend upgrading to a newer product. For example, Microsoft Windows 7 is a legacy system no longer receiving support.
5. Training employees
Employees are your first line of defence against cyberattacks and are constantly in the thick of it, making some form of cybersecurity training a critical expense. However, without proper awareness, they may also become the first victims of human error, particularly in high-risk situations and remote work environments.
Unsecured connections and lax access controls to sensitive company accounts can provide cybercriminals with easy entry points. To mitigate these risks, employees should be trained on essential cybersecurity topics, including:
- Recognising common threats like scams, phishing, ransomware, and shady emails.
- Implementing protective measures such as MFAs.
- Following business-specific policies, such as validating invoices.
- Responding effectively in the event of a cyber emergency.
Consult with IT experts today
Equipping employees with these skills ensures they remain vigilant and prepared, strengthening your business's defence about the latest cyber security threats. If you have any questions not addressed in this article, feel free to contact us—our helpdesk is always ready to help you.
And maybe consider subscribing to our monthly IT Essentials Digest, where we deep-dive into particular subjects of interest to every small business owner.
Next month, join us as we explore the benefits and economies of: Managed IT Support (Theme: Stress-Free IT)